You may have seen the announcement – we can now configure Dataverse IP Firewall per managed environment:
https://learn.microsoft.com/en-us/power-platform/admin/ip-firewall#what-is-audit-only-mode
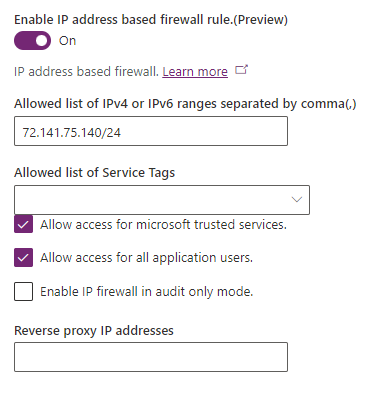
This is only possible in the managed environments, so all the licensing and other considerations still apply.
Also, when specifying the IP address, you actually need to use CIDR format (classless inter-domain routing), which looks like this:
192.168.0.15/24
That extra number (24 in my example) indicates network identifier bits, so all ip addresses in that network will be allowed. In the example above, 192.168.0.15 and 192.168.0.15 would both be allowed, just like any other 192.168.0.X address.
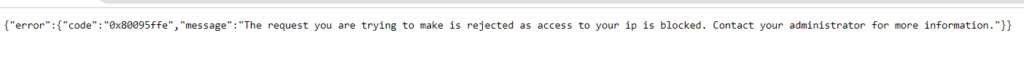
IP Firewall settings apply to Dataverse, not to the Power Platform in general. So, for instance, if you try using a model-driven application once the Firewall is on and you IP address gets blocked, you’ll see a message like this:
However, you can still use Canvas Apps (I am assuming that’s for as long as those apps are not trying to access Dataverse from the blocked IP addresses).
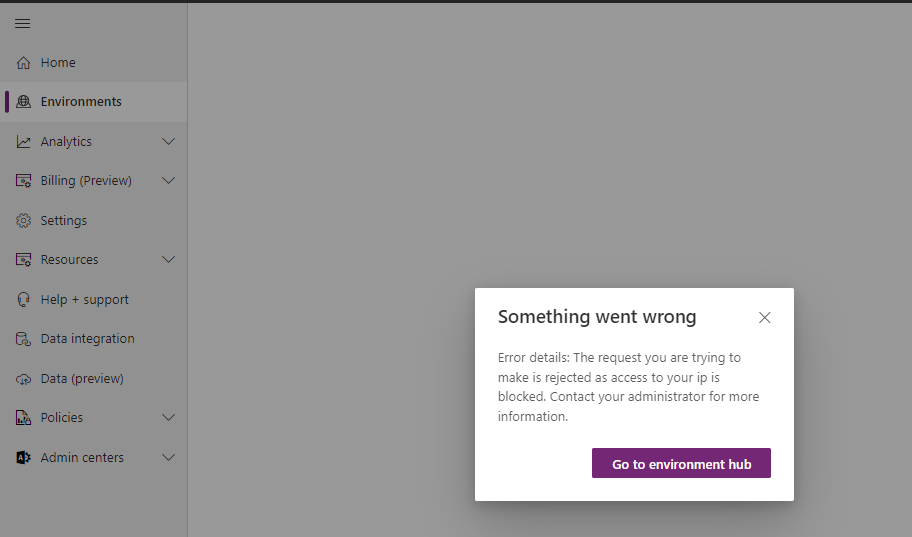
You might also get your own IP address blocked, in which case you would loose access to the environment settings tab, which is, of course, quite a bummer:
Try not to do that, but, if you do, you may be able to resolve this unexpected problem by updating your organization settings through a Power Automate flow – that’s assuming you kept flows allowed when enabling IP Firewall:
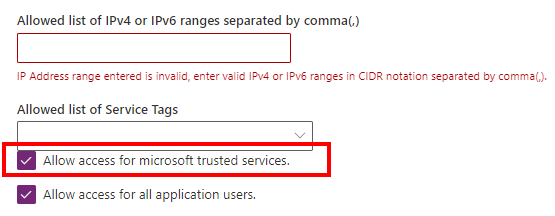
Well, assuming you kept it enabled, you can create a flow similar to the one below in your environment:
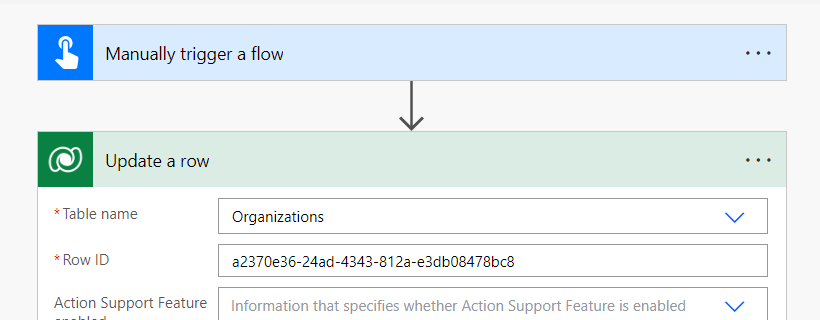
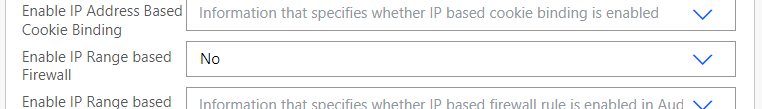
Create a new flow, configure it as per the screenshots above, runt it… and you’ll be able to use your environment again.