What are Data Loss Prevention polices in Power Platform and why would you use those?
That’s the question I had to answer recently in a relatively concise manner, and, perhaps, what came out could be useful for others, too.
Essentially, the purpose of DLP in Power Platform is to help prevent users from unintentionally exposing organizational data.
DLP-s take care of one common scenario where such an exposure may happen. Since Power Platform in general, and Power Automate / Canvas Apps in particular rely heavily on the concept of data connectors, those connectors are meant to be combined in the same Power Automate flows/canvas applications.
When two or more connectors are combined that way, sensitive data available through one connector might be unintentionally exposed through the other connector.
In the extreme example, imagine SIN numbers stored in the Dataverse database, and imagine a Power Automate flow utilizing both Dataverse and Twitter connectors, where some information would be pushed to Twitter in response to certain events in Dataverse.
If, for whatever reason, sensitive data (SIN in this example) were exposed on Twitter, there might be implications, and the easiest way to prevent this from happening would be to ensure that only specific connectors are allowed to be used together in the same flows and /or apps.
Implementing that kind of protection is exactly what Data Loss Prevention policies in Power Platform are meant for.
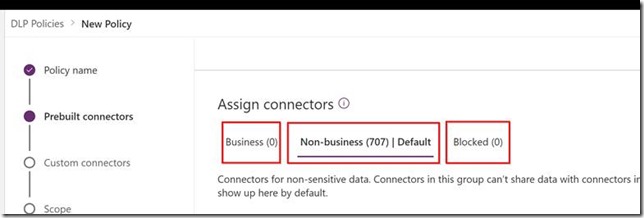
Any DLP policy in Power Platform environment will be splitting conectors into 3 different categories:
– Business
– Non-business
– Blocked
As soon as a DLP has been applied to the Power Platform environment, connectors from Business and Non-Business categories can’t be mixed in the same flows/apps. And, of course, blocked connectors will be blocked.
DLP policies can be combined, and, when it’s done, the most restrictive ones will apply to any combination of data conectors.
For example, if there are 9 polices which have all identified Sharepoint and Twitter as non-business connectors, Power Automate flows using both connectors will still be running fine.
However, if a new policy were added which would turn Sharepoint into a “business” connector, all those existing flows would stop working.
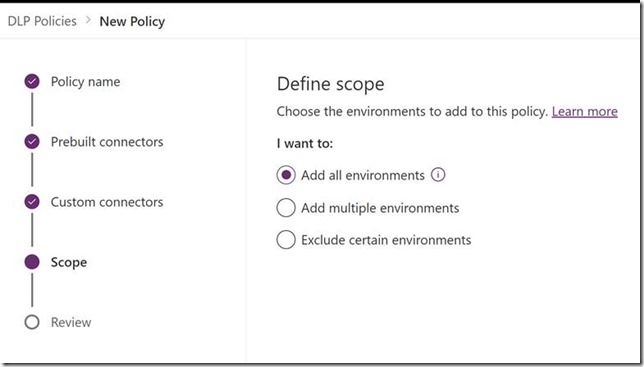
There are different ways to apply DLP policies.
They can be applied to all environments, they can be applied to the specific environments only, or they can be applied to all environments with the exception of a few:
On top of that, there are a few additional considerations.
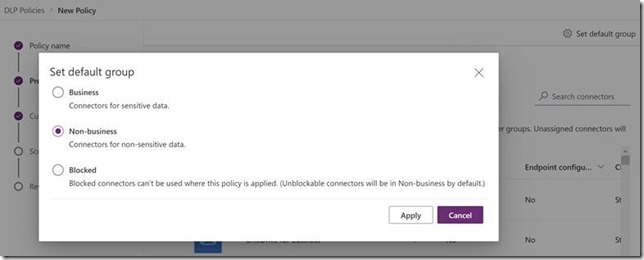
DLP polices can treat new pre-built connectors differently by default:
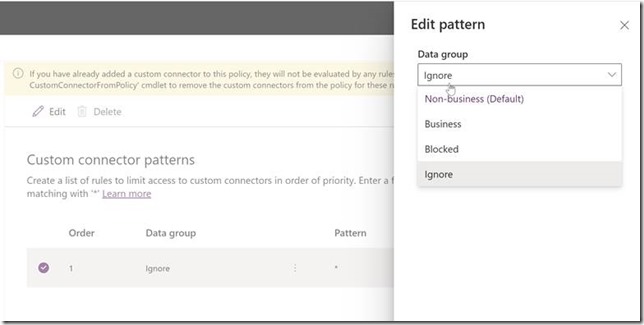
Rules for adding custom connectors can be configured separately for each DLP:
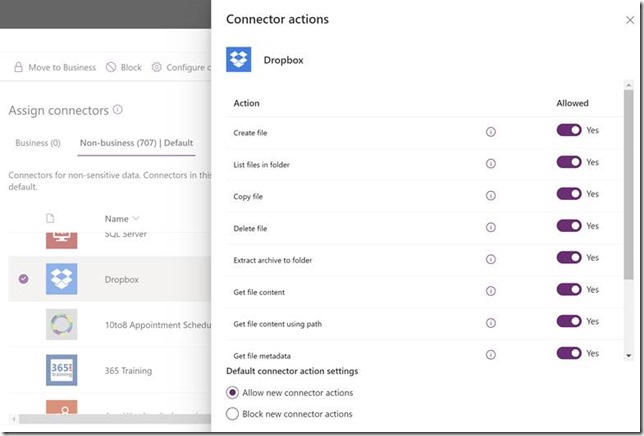
Certain connectors can be configured in a more granular manner to allow/disallow specific connector actions:
And the rest would be all about setting it up. Want to know more? Have a look at the docs: https://docs.microsoft.com/en-us/power-platform/admin/wp-data-loss-prevention